June 11th, 2024
It’s been a week since we announced FileCloud’s acquisition of Signority! As we continue to navigate this transition, we want to assure all Signority customers of our commitment to them. We are focused on maintaining the transparent and open communication that we value so highly here at Signority.
In the following blog post, Jane He, our founder and new SVP of the Signority Business Unit will address some of the concerns and questions our customers have brought to us, while outlining our strategies to continue ensuring excellence and reliability of Signority.
Data Sovereignty
With this acquisition, Signority remains committed to data sovereignty, particularly when it comes to hosting data centers in Canada. We understand the importance of local data handling for our Canadian customers, and we see this as a pivotal opportunity for our customers concerned with data sovereignty to also have the opportunity to leverage FileCloud’s robust on-premises deployment options. We remain dedicated to keeping your data secured within Canadian borders—aligning with regulatory requirements—while continuing to provide our customers with the peace of mind of knowing their data is protected.
Clarification of Signority’s Status
We want to clarify that Signority remains a proudly Canadian entity, fully operational within Canada, while functioning as a separate subsidiary of FileCloud. This status reinforces our foundational ties to Canadian values and business practices, ensuring that our operations, management, and data governance continue to meet the expectations and regulations specific to Canada.
Customer Support
We understand that our customers have a strong preference for local customer support, and we are committed to maintaining our Canadian-based customer support operations while also integrating with FileCloud’s 24/7 global support framework. This hybrid approach will enhance our responsiveness and ability to address your needs quickly and effectively, ensuring the support you need is available whenever and wherever you need it.
Moving Forward
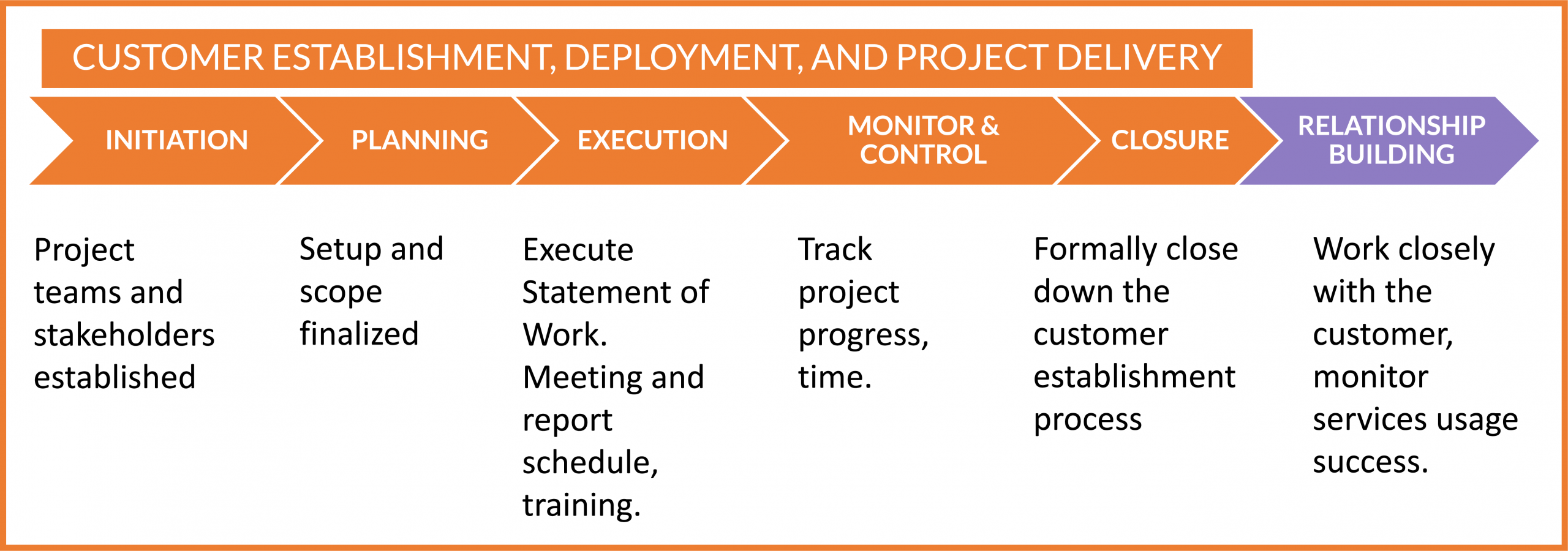
In the coming weeks, the team at Signority will continue to engage with you through various channels. This will include a scheduled Product Marketing meeting in June (details to follow) led by Jason Dover—FileCloud’s CPO— to discuss these topics in greater depth. We also plan to send out a detailed customer letter reiterating these points and more, ensuring that you remain fully informed and confident in the direction we are heading.
Thank you for your continued trust and partnership. We are excited about the future and are committed to growing together, delivering solutions that not only meet but exceed your expectations.
Your success is our success, and we look forward to achieving great things together.
Stay tuned for further updates, and as always, we value your feedback and welcome any questions you may have via our Contact Form.
Jane He
SVP, Signority Business Unit